CYBER SECURITY CONSULTING SERVICE AWARDS AND RECOGNITIONS
CyberSecOp's comprehensive managed security services, cyber security consulting, professional services, and data protection technology are recognized as industry-leading threat detection and response solutions by major analyst firms, key media outlets, and others.
Using Linux Won't Save You from Ransomware - Here's Why
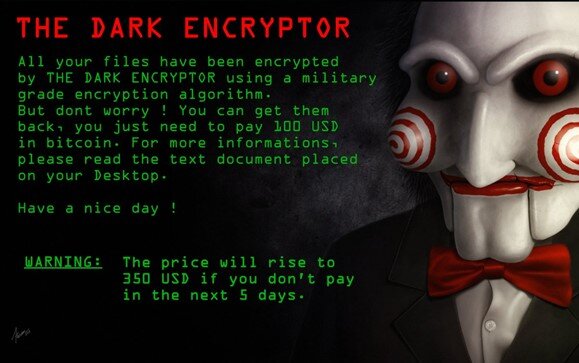
"Ransomware attacks are becoming more targeted, sophisticated, and costly, even as the overall frequency of attacks remains consistent." (FBI, 2019)
Since early 2018, there has been a sharp spike in the cleverness, thoroughness, and precision of the security breaches we see in the ransomware landscape. Regardless of attack vector - whether it's from phishing, vishing, or the classic insider threat - once ransomware is on your computer, it's incredibly difficult to restore your files. It takes some serious intervention to stand a chance of recovering your business (or personal) data.
The easiest solution is to get the appropriate key and decryption tool, and use them together to unlock your files...but typically you only receive those resources in exchange for paying the ransom, and many companies can’t afford the ransom at its original price. By that time, there's a good chance you've taken a catastrophic financial blow. From hospitals, to insurance companies, to banks, there are plenty of highly valuable (and highly vulnerable) assets to be manipulated, and threat actors don’t hesitate to put lives at stake for the benefit of their wallets.
So how can we prevent these breaches? What is the key to staying safe from attackers?
The answer may be simpler than you think.
The three most impactful measures you can take to stay safe are as follows:
★ Quarantine
○ Take your computer off the network or wifi and reset your data by wiping the device entirely back to its factory settings (the way it came when you bought it) the moment you can confirm there has been a breach.
★ Have a backup
○ You can only take the first measure if you either don’t care at all about your data, or you have bothered to back it up so you have an unencrpted copy.
★ Get help negotiating your ransom down
○ If you need to pay the threat actor the ransom money to recover your data, there are many firms that can help you with this - don’t pay the full price of the ransom! Firms that can help with ransom negotiation and essential protections include CyberSecOp, which you can reach by using Our Contact Form.
So what’s so special about the threat of Linux-based malware? A Linux-based ransomware variant has the potential to take down any and every industry. Major cloud providers like AWS (Amazon Web Services), Oracle, and Microsoft base entire workloads on Linux; malware sweeping through those servers could bring down any company that uses a modernized cloud stack to host their sites and data.
And then there are hacktivists - hackers who hack to do activism for their cause (which can vary greatly in scope between organizations). Hacktivists have a history of using their ransomware attacks to make a point - whether it’s political or personal - and to incite fear in other companies or individuals who support the cause represented by the victim. While you might not think this presents a threat to you personally, or even to your business, the truth is that innovations in cyberattacks threaten us all. If the target were to have a Linux-based system, the hacktivist group targeting that individual would be devoted to finding a way to spread ransomware across Linux-based devices. When ransomware is evolved by perpetrators to this degree, we are likely to see major outages across all the cloud providers listed above, and it could cripple any business or personal account that is hosted therein.
To avoid such a catastrophic and monolithic problem, we should learn to govern our systems from a more ecosystem-centric approach, rather than depend on the classic signature-based antivirus alerts that have become standard. You may recognize Norton Antivirus alerts or even operating-system-based protection like Windows Defender presenting to you pop-ups about updating your signatures.
The truth is that we shouldn’t rely on the technical drivers of these updates, the people who hunt down and publish these known virus signatures, to keep us safe. We should be educating our employees, friends, and families, on the essentials of how to stay digitally secured and prevent breaches in the modern threat landscape. This concept is especially important as a mere tweak in the code of a virus and a quick recompilation of that code can cause the hash (or signature) of the virus to change, causing these famous signature-based antivirus softwares to completely miss the threat on your device.
A phenomenal example of how dangerous this variant-based workaround can be is what happened to the Colorado State Department of Transportation (CDOT) in early 2018.
“As CDOT’s Information Security group scrambled to contain the spread and impact of SamSam’s first wave, their efforts were quickly undermined by another variant of the same ransomware strain that was spreading throughout many of the newly sanitized zones of their network.”[1] (Richard Horne for the SANS Institute)
In an interview with the Denver Post, Brandi Simmons, a spokeswoman for the state's Office of Information Technology said, “The variant of SamSam ransomware just keeps changing. The tools we have in place didn't work. It's ahead of our tools.” The tools in question were signature-tracking antivirus software, like what many of us use on our home computers. In the end, Colorado's Office of Information Technology, the Colorado National Guard, and the FBI all had to collaborate to contain this threat, and by the time they had, over 2,000 computers running Windows and McAfee security software had been taken offline.
In conclusion, it seems inevitable that we will see Linux systems fall prey to the same types of ransomware we currently battle; it’s only a matter of time. Make sure you’re safe and you know how to protect your data: maintain a backup of all your files, be ready to quarantine in the event of a breach, and remember not to panic. We are here to help.
Sources:
https://www.sans.org/reading-room/whitepapers/tools/strings-me-linux-ransomware-39870
https://www.darkreading.com/attacks-breaches/second-ransomware-round-hits-colorado-dot/d/d-id/1331197
Authored by Alison Stuart
What is Cyber Security, IT Security, and Data Security?
What is the need for IT security and CyberSecurity?
Computer security, cybersecurity or information technology security (IT security) is the protection of computer systems and networks from the theft of or damage to their hardware, software, or electronic data, as well as from the disruption or misdirection of the services they provide.
IT security is a set of cybersecurity strategies that prevents unauthorized access to organizational assets such as computers, networks, and data. It maintains the integrity and confidentiality of sensitive information, blocking the access of sophisticated hackers.
What is Data Security?
Data security means protecting digital data, such as those in a database, from destructive tampering and unauthorized access. Hardware based security or assisted computer security offers an alternative to software-only computer security.
Common examples of:
- Data encryption
- Tokenization
- Key management
- Data loss prevention
- Data classification
- Data accees management
What is the need for network security?
Network security is the practice of securing a computer network from intruders, whether targeted attackers or opportunistic malware. Application security focuses on keeping software and devices free of threats. A compromised application could provide access to the data its designed to protect.
What is Internet security
Internet security involves the protection of information that is sent and received in browsers, as well as network security involving web-based applications. These protections are designed to monitor incoming internet traffic for malware as well as unwanted traffic. This protection may come in the form of firewalls, antimalware, and antispyware.
What is Critical infrastructure security:
Critical infrastructure security consists of the cyber-physical systems that modern societies rely on.
Common examples of critical infrastructure:
- Electricity grid
- Water purification
- Traffic lights
- Shopping centers
- Hospitals
What is Application security:
You should choose application security as one of the several must-have security measures adopted to protect your systems. Application security uses software and hardware methods to tackle external threats that can arise in the development stage of an application.
Applications are much more accessible over networks, causing the adoption of security measures during the development phase to be an imperative phase of the project.
Types of application security:
- Software development
- Application testing
- Code review
- Vunerablity and penetration testing
What is Network security:
Network security ensures that internal networks are secure by protecting the infrastructure and inhibiting access to it.
Common examples of network security implementation:
- Extra logins
- New passwords
- Application security
- Antivirus programs
- Antispyware software
- Encryption
- Firewalls
- Monitored internet access
Types of cyber threats:
The threats countered by cyber-security are three-fold:
Cybercrime includes single actors or groups targeting systems for financial gain or to cause disruption.
Cyber-attack often involves politically motivated information gathering.
Cyberterrorism is intended to undermine electronic systems to cause panic or fear.
So, how do malicious actors gain control of computer systems? Here are some common methods used to threaten cyber-security:
Malware
Malware means malicious software. One of the most common cyber threats, malware is software that a cybercriminal or hacker has created to disrupt or damage a legitimate user’s computer. Often spread via an unsolicited email attachment or legitimate-looking download, malware may be used by cybercriminals to make money or in politically motivated cyber-attacks.
There are a number of different types of malware, including:
Virus: A self-replicating program that attaches itself to clean file and spreads throughout a computer system, infecting files with malicious code.
Trojans: A type of malware that is disguised as legitimate software. Cybercriminals trick users into uploading Trojans onto their computer where they cause damage or collect data.
Spyware: A program that secretly records what a user does, so that cybercriminals can make use of this information. For example, spyware could capture credit card details.
Ransomware: Malware which locks down a user’s files and data, with the threat of erasing it unless a ransom is paid.
Adware: Advertising software which can be used to spread malware.
Botnets:Networks of malware infected computers which cybercriminals use to perform tasks online without the user’s permission.
SQL injection
An SQL (structured language query) injection is a type of cyber-attack used to take control of and steal data from a database. Cybercriminals exploit vulnerabilities in data-driven applications to insert malicious code into a databased via a malicious SQL statement. This gives them access to the sensitive information contained in the database.
Phishing
Phishing is when cybercriminals target victims with emails that appear to be from a legitimate company asking for sensitive information. Phishing attacks are often used to dupe people into handing over credit card data and other personal information.
Man-in-the-middle attack
A man-in-the-middle attack is a type of cyber threat where a cybercriminal intercepts communication between two individuals in order to steal data. For example, on an unsecure WiFi network, an attacker could intercept data being passed from the victim’s device and the network.
Denial-of-service attack
A denial-of-service attack is where cybercriminals prevent a computer system from fulfilling legitimate requests by overwhelming the networks and servers with traffic. This renders the system unusable, preventing an organization from carrying out vital functions.
8 Cyber Security Best Practices for Business
- Conduct Phishing Simulations
- Implement Risk Management Governance Approach
- Secure Remotely Working and Travelling Employees
- Plan for mobile devices
- Create a Cybersecurity Awareness Training Program
- Monitor User and File Activity
- Enforce password best practices
- Enforce the Use of Password Managers, SSOs, and MFAs
- Audit Privileged Access
- Implement Data Loss Prevention
- Update Software and Systems
- Implement and monitor EDR, MDR, and SIEM
- Regularly back up all data, and offsite backup
CyberSecOp cybersecurity solution provide pace of mind when it comes to privacy and security. Ensuring data security in the cloud or onpfremisies , compliant and protected by best-in-class security: your data, and the tools you use to harness it, can truly empower your business.