CYBER SECURITY CONSULTING SERVICE AWARDS AND RECOGNITIONS
CyberSecOp's comprehensive managed security services, cyber security consulting, professional services, and data protection technology are recognized as industry-leading threat detection and response solutions by major analyst firms, key media outlets, and others.
Ransomware Attack: Threats, and Countermeasures
When you combine cryptography with malware, you get a very dangerous mix of problems. This is a type of computer virus that goes by another name, “ransomware”. This type of virus is part of a field of study called “cryptovirology”. Through the use of techniques called phishing, a threat actor sends the ransomware file to an unknowing victim. If the file is opened it will execute the virus payload, which is malicious code. The ransomware runs the code that encrypts user data on the infected computer or host. The data are user files like documents, spreadsheets, photos, multimedia files and even confidential records. The ransomware targets your personal computer files and applies an encryption algorithm like RSA which makes the file inaccessible. The only way to access them is if the user pays a ransom to the threat actor by following instructions which appear encoded into the encrypted files. Thus it is called ransomware, because a form of payment is demanded in order to fix the problem.
Once they have all publicly available email addresses, the fun starts. The more of your email addresses that are floating out there, the bigger your attack footprint is, and the higher the risk is. It’s often a surprise how many addresses are actually out there. Now they can send all employees an email supposedly coming from Accounting, Human Resources, the CEO or perhaps the mail room, and social engineer your users to click on a link. almost 90 percent of attack are done via the internet, based on the new software model, and yes the bad guys are also moving to the cloud. Software is shifting away from locally-installed apps to Software as a Service web applications that run in the cloud. Criminals are cashing in on this trend, which has led to the creation of Ransomware as a Service (RaaS), a growing threat to business.
RaaS refers to various online malware exploits that bad actors can use to attack the IT assets of businesses and individuals. These attack programs are created by criminal entrepreneurs who sell their services to other criminals. The people who buy these programs then extort or blackmail their victims by holding computer systems to ransom.
How does Ransomware spread?
Ransomware is typically spread through phishing emails that contain malicious attachments. These emails appear to come from a legitimate source and give a compelling reason that the document is important. Malicious attachments are often PDF, ZIP, DOC, XLS, PPT files that appear as invoices, legitimate business documents, or other work-related files. In some cases, Ransonware may end up on your computer by visiting infected web sites. To avoid malicious drive-by downloads, ensure that antivirus and all installed software is up-to-date.
How to Mitigate the Risk of Ransomware Infections
These recommendations are not comprehensive but provide general best practices.
Securing Networks and Systems
Have an incident response plan that includes what to do during a ransomware event.
Backups are critical. Use a backup system that allows multiple iterations of the backups to be saved, in case a copy of the backups includes encrypted or infected files. Routinely test backups for data integrity and to ensure it is operational.
Use antivirus and anti-spam solutions. Enable regular system and network scans with antivirus programs enabled to automatically update signatures. Implement an anti-spam solution to stop phishing emails from reaching the network. Consider adding a warning banner to all emails from external sources that reminds users of the dangers of clicking on links and opening attachments.
Disable macros scripts. Consider using Office Viewer software to open Microsoft Office files transmitted via e-mail instead of full office suite applications.
Keep all systems patched, including all hardware, including mobile devices, operating systems, software, and applications, including cloud locations and content management systems (CMS), patched and up-to-date. Use a centralized patch management system if possible. Implement application white-listing and software restriction policies (SRP) to prevent the execution of programs in common ransomware locations, such as temporary folders.
Restrict Internet access. Use a proxy server for Internet access and consider ad-blocking software. Restrict access to common ransomware entry points, such as personal email accounts and social networking websites.
Apply the principles of least privilege and network segmentation. Categorize and separate data based on organizational value and where possible, implement virtual environments and the physical and logical separation of networks and data. Apply the principle of least privilege.
Vet and monitor third parties that have remote access to the organization’s network and/or your connections to third parties, to ensure they are diligent with cybersecurity best practices.
Participate in cybersecurity information sharing programs and organizations, such as MS-ISAC and InfraGard.
Securing the End User
Provide social engineering and phishing training to employees. Urge them not to open suspicious emails, not to click on links or open attachments contained in such emails, and to be cautious before visiting unknown websites.
Remind users to close their browser when not in use.
Have a reporting plan that ensures staff knows where and how to report suspicious activity.
Responding to a Compromise/Attack
Immediately disconnect the infected system from the network to prevent infection propagation.
Call CyberSecOp.com Ransomware Response Team: They provide remediation and bitcoin payment services.
Determine the affected data as some sensitive data, such as electronic protected health information (ePHI) may require additional reporting and/or mitigation measures.
Determine if a decryptor is available. Online resources such as No More Ransom! can help.
Restore files from regularly maintained backups.
Report the infection. It is highly recommended that SLTT government agencies report ransomware incidents to MS-ISAC. Other sectors and home users may report to infections to local Federal Bureau of Investigation (FBI) field offices or to the Internet Crime Complaint Center (IC3).
Ransomware Checker & Removal Tools
Addressing Cyber Threats and Enabling Security in your Enterprise
Cybersecurity threats from hacktivists, criminals, and hostile nation states are enough to keep government officials, businesses, and consumers up at night. These attacks are growing in sophistication and frequency and pose serious threats to our national and economic security.
Everyone impacted by these vicious and dangerous acts must work together to help prevent, protect against, and effectively respond to them.
What are the biggest cyber threats CISOs are worried about in 2019? In today's age of breaches, staying ahead of cyber threats is becoming more critical than ever. Dive into how organizations are addressing the threat of cyber attacks, how they are measuring risk, and what they are doing about improving security from some of the top experts in the field.
Ransomware is still a large risk, affecting a large number of businesses
Data Loss and Data Breach based on information available on dark web, proves that organization can’t protect customers data.
Small business with no security program are at risk more than large organization.
All industry need to have some type of cyber regulations based on secure standards such as NIST or ISO.
What can business do, to enable a stronger security posture in their enterprise
Businesses adopt standalone cyber insurance policies as boards and executives wake up to cyber liability. As boards and executives experience and witness the impact of cyber attacks, including reduced earnings, operational disruption, and claims brought against directors and officers, businesses will turn to tailored enterprise cyber insurance policies, rather than relying on “silent” components in other policies. Adoption will spread beyond traditional buyers of cyber insurance, such as retail, financial, and healthcare sectors, to others vulnerable to cyber-related business disruption, including manufacturing, transportation, utility, and oil and gas.
As the physical and cyber worlds collide, chief risk officers take center stage to manage cyber as an enterprise risk. As sophisticated cyber attacks generate real-world consequences that impact business operations at increasing scale, C-suites will wake up to the enterprise nature of cyber risk. In 2018, expect CROs to have a seat at the cyber table, working closely with chief information security officers (CISOs) to help organizations understand the holistic impact of cyber risk on the business.
Regulatory spotlight widens and becomes more complex, provoking calls for harmonization. EU holds global companies to account over General Data Protection Regulation (GDPR) violation; big data aggregators come under scrutiny in the U.S. In 2018, regulators at the international, national and local levels will more strictly enforce existing cybersecurity regulations and introduce new regulations. Expect to see EU regulators holding major U.S. and global companies to account for GDPR violations. Across the Atlantic, big data organizations (aggregators and resellers) will come under scrutiny on how they are collecting, using, and securing data. Industry organizations will push back on regulators, calling for alignment of cyber regulations.
Criminals look to attack businesses embracing the Internet of Things, in particular targeting small to mid-sized businesses providing services to global organizations. In 2018, global organizations will need to consider the increased complexities when it comes to how businesses are using the IoT in relation to third-party risk management. The report predicts large companies will be brought down by an attack on a small vendor or contractor that targets the IoT, using it as a way into their network. This will serve as a wake-up call for large organizations to update their third-party risk management, and for small and mid-sized businesses to implement better security measures or risk losing business.
As passwords continue to be hacked, and attackers circumvent physical biometrics, multi-factor authentication becomes more important than ever before. Beyond passwords, companies are implementing new methods of authentication – from facial recognition to fingerprints. However, these technologies are still vulnerable and as such, the report anticipates that a new wave of companies will embrace multi-factor authentication to combat the assault on passwords and attacks targeting biometrics. This will require individuals to present several pieces of evidence to an authentication instrument. With the new need for multi-factor authentication, and consumer demand for unobtrusive layers of security, expect to see the implementation of behavioral biometrics.
Criminals will target transactions that use reward points as currency, spurring mainstream adoption of bug bounty programs: Companies beyond the technology, government, automotive and financial services sectors will introduce bug bounty platforms into their security programs. As criminals target transactions that use points as currency, businesses with loyalty, gift and rewards programs –such as airlines, retailers, and hospitality providers– will be the next wave of companies implementing bug bounty programs. As more organizations adopt the programs, they will require support from external experts to avoid introducing new risks with improperly configured programs.
Ransomware attackers get targeted; crypto currencies help ransomware industry flourish. In 2018, ransomware criminals will evolve their tactics. The reports predicts that attackers utilizing forms of benign malware—such as software designed to cause DDoS attacks or launch display ads on thousands of systems— will launch huge outbreaks of ransomware. While attackers will continue to launch scatter-gun-style attacks to disrupt as many systems as possible, the report predicts an increase in instances of attacks targeting specific companies and demanding ransomware payments proportional to the value of the encrypted assets. Crypto currencies will continue to support the flourishing ransomware industry overall, despite law enforcement becoming more advanced in their ability to trace attacks, for example through bitcoin wallets.
Insider risks plague organizations as they underestimate their severe vulnerability and liability while major attacks fly under the radar. In 2017, businesses under invested in proactive insider risk mitigation strategies, and 2018 will be no different. According to the report, a continued lack of security training and technical controls, coupled with the changing dynamics of the modern workforce, the full extent of cyber attacks and incidents caused by insiders will not become fully public. Many companies will continue to reactively responding to incidents behind closed doors and remain unaware of the true cost and impact of insider risk on the organization.
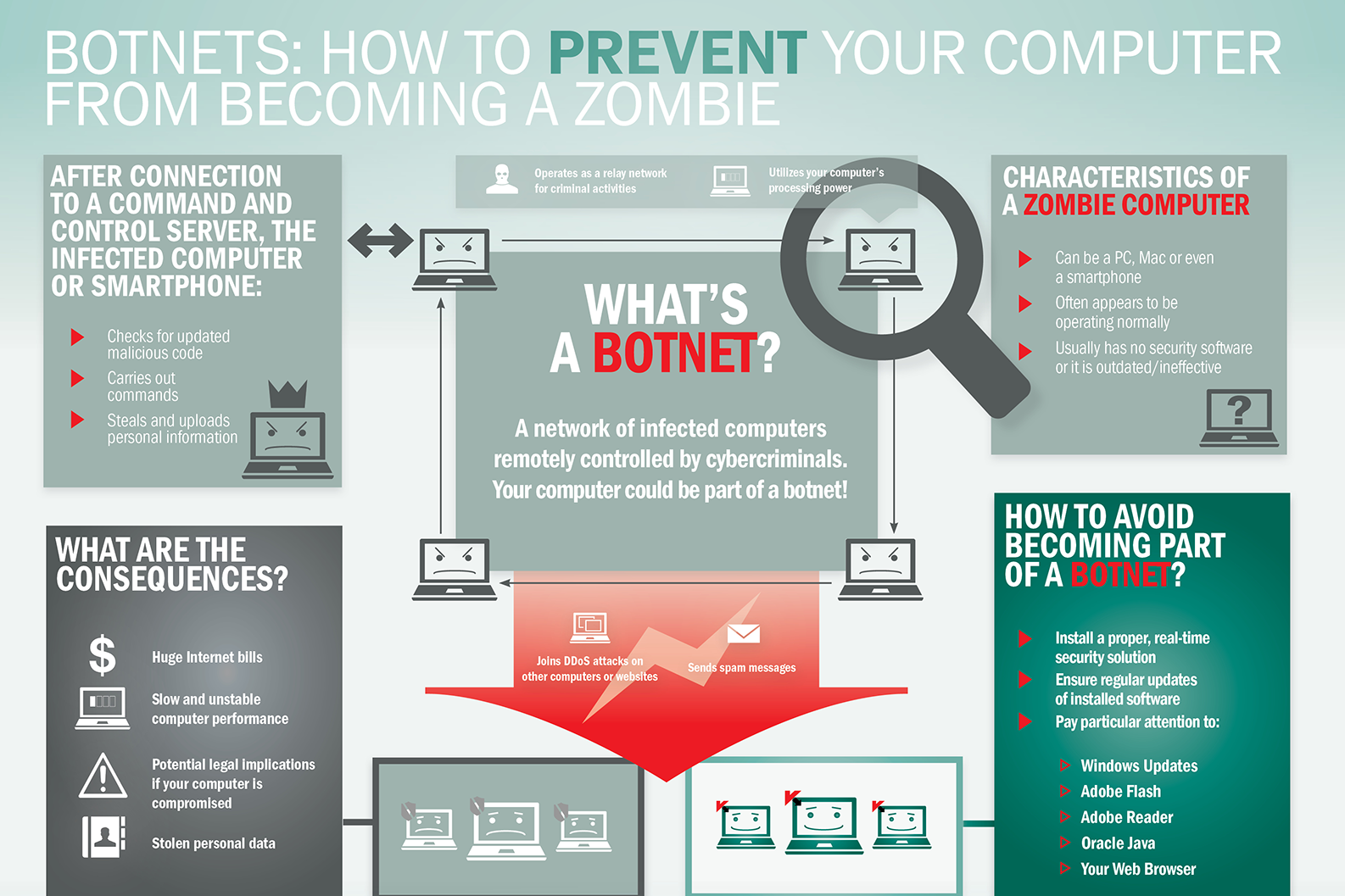
What is Botnet - Cybercriminals #1 Weapon
The word Botnet is formed from the words ‘robot’ and ‘network’. Cybercriminals use special Trojan viruses to breach the security of several users’ computers, take control of each computer and organise all of the infected machines into a network of ‘bots’ that the criminal can remotely manage.
Botnet Prevention- What is Botnet
How Botnets can impact you
Often, the cybercriminal will seek to infect and control thousands, tens of thousands or even millions of computers – so that the cybercriminal can act as the master of a large ‘zombie network’ – or ‘bot-network’ – that is capable of delivering a Distributed Denial of Service (DDoS) attack, a large-scale spam campaign or other types of cyberattack.
In some cases, cybercriminals will establish a large network of zombie machines and then sell access to the zombie network to other criminals – either on a rental basis or as an outright sale. Spammers may rent or buy a network in order to operate a large-scale spam campaign.
How to prevent your computer becoming part of a Botnet
Installing effective anti-malware software will help to protect your computer against Trojans and other threats.
Businesses Expansion of Attack Surfaces
One of the main reasons cyber risk increases exponentially is the rapid expansion of attack surfaces. In these places, software programs are vulnerable to attack or probe by an adversary. According to the SANS Institute, attack surfaces can include any part of a company’s infrastructure that exposes its networks and systems to the outside, from servers and open ports to SQLs, email authentication, and even employees with “access to sensitive information.” It can also include user input via keyboard or mouse, network traffic, and external hardware that is not protected by cyber hardening technology.
It would be easy to blame the Internet of Things (IoT) for expanding attacks, as Intel projects two billion smart devices worldwide by 2020. But in reality, the IoT is only part of the attack surface epidemic.
According to Cybersecurity Ventures, there are now 111 billion new lines of code written each year, introducing vulnerabilities both known and unknown. Not to be overlooked as a flourishing attack vector are humans, which some argue are both the most important and the weakest link in the cyberattack kill chain. In fact, in many cybersecurity circles, there is a passionate and ongoing debate regarding just how much burden businesses should put on employees to prevent and detect cyber threats. However, what is not up for debate open is just how vulnerable humans are to intentionally or unintentionally open the digital door for threat actors to walk in. This is most evident because 9 out of 10 cyberattacks begin with some form of email phishing targeting workers with mixed levels of cybersecurity training and awareness.
Critical Infrastructure Protection Remains a Challenge
Critical infrastructure, often powered by SCADA systems and equipment now identified as part of the Industrial Internet of Things (IIoT), is a significant contributor to attack surface expansion. Major attacks targeting these organizations occur more from memory corruption errors and buffer overflows exploits than from spear-phishing or email spoofing and tends to be the motive of nation-states and cyber terrorists more so than generic hackers.
“Industrial devices are designed to have a long life span, but most legacy equipment still in use was not originally built to achieve automation and connectivity.” The IIoT does provide many efficiencies and cost-savings benefits to companies in which operational integrity, confidentiality, and availability are of the utmost importance. Still, introducing technology into heavy machinery and equipment that wasn’t built to communicate outside of a facility has proven challenging. The concept of IT/OT integration, which is meant to merge the physical and digital security of corporations and facilities, has failed to reduce vulnerabilities in a way that significantly reduces risk. As a result, attacks seeking to exploit critical infrastructure vulnerabilities, such as WannaCry, have become the rule and not the exception.
To date, ARE CYBERCRIMINALS winning?
Critical infrastructure cybersecurity has relied too much upon network monitoring and anomaly detection to detect suspicious traffic before it turns problematic. The challenge with this approach is that it is reactionary and only effective after an adversary has breached some level of defense.
We take an entirely different approach, focusing on prevention by denying malware the uniformity it needs to propagate. We use a binary randomization technique that shuffles the basic constructs of a program, known as basic blocks, to produce functionally identical code but legally unique. When an attacker develops an exploit for a known vulnerability in a program, it is helpful to know where all the code is located so that they can repurpose it to do their bidding. Binary randomization renders that prior knowledge useless, as each instance of a program has code in different locations.
One way to visualize the concept of binary randomization is to picture the Star Wars universe at the time when Luke Skywalker and the Rebel Alliance set off to destroy the Death Star. The Rebel Alliance had the blueprints to the Death Star and used those blueprints to find its only weakness. Luke set off in his X-Wing and delivered a proton torpedo directly to the weak spot in the Death Star, destroying it. In this scenario, the Death Star is a vulnerable computer program, and Luke is an adversary trying to exploit said computer program.
Now imagine that the Galactic Empire built 100 Death Stars, protected by RunSafe’s new Death Star Weakness Randomization. This protection moves the weakness to a different place on each Death Star. Now imagine you are Luke, flying full speed toward the flaw in the Death Star, chased by TIE fighters, only to find that the weakfaultnot where the blueprint showed. The Rebel attack fails, and the Galactic Empire celebrates by destroying another planet. Like the Death Star scenario above, code protected with binary randomization will still contain vulnerabilities. Still, an attacker’s ability to successfully exploit that vulnerability on multiple targets becomes much more difficult.
Ransomware campaign up around the world
A new email ransomware campaign is spreading around the world. Researchers at Fortinet say it’s a spam effort, meaning the messages are not targeted. Instead they are addressed generally, like “Dear customer.” The subject line in the email would be something like “Document number…”, “Your order number” or “Ticket number.” With the email is a malicious attachment that leads to the installation of malware. The initial targets are corporate mail servers used to forward this email. These have been found in Canada, the U.S. the United Kingdom and other countries.
The best defense against ransomware – or any email-delivered malware – is to watch out for it. Be cautious about unsolicited emails, especially those with attachments. And it’s vital you always have a separate backup of your data made it a way that can’t be infected, just in case you make a mistake.
Meanwhile McAfee reports some Canadian organizations have been victimized by a separate operation. A group security that researchers call Hidden Cobra, believed to be backed by North Korea, has been putting surveillance software on the systems of companies. The suspicion is the Canadian victims have been used as listening or data relay points. The malware that this campaign has installed has not stolen financial or sensitive data but appears to be there find out what’s on a computer, and be ready to launch further attacks.
Companies have to make sure their systems have the latest security patches. In addition, because the malware appears to be distributed through email, employees have to be reminded to be careful on what they click on.
For more on this see my story today on ITWorldCanada.com.
The U.S. National Security Agency has just suffered a black eye from an international standards body. According to a blog on Bitdefender, the International Organization of Standardization – known more commonly as ISO – rejected two new encryption algorithms suggested by the NSA to secure Internet of Things devices. The algorithms would scramble information on Internet-connected devices like home surveillance cameras and toys. But the NSA’s reputation for creating tools to hack into applications apparently give it a bad name at the ISO. One ISO delegate accused the NSA of telling half-truths and lies in its presentation.
If that allegation is accurate, it isn’t good. Internet of Things devices badly need better security. People and companies around the world buy tens of thousands of them a year. Insecure devices don’t improve security.
That’s it for Cyber Security Today. Subscribe on Apple Podcasts, Google Play, or add us to your Alexa Flash Briefing. Thanks for listening.
Cyber Security Developments
Cyber Security Is The Backbone Any Online Businesses – Here Are Some Quick Tips To Keep Yourself Informed About The Latest Threats Surrounding Your Business.
Cyber Security Developments
Within a standard nine to five working day, it’s said that there are almost two million data records lost or stolen. Cybercrime has become something of an epidemic in recent years – and it’s no exaggeration to say that everyone is at risk.
Hackers operate in an increasingly complex way and are happy to target small businesses and individuals, who are most likely to be vulnerable to attack. The nature of the threat changes as technology advances and so the only way to stay safe is to stay up to date.
But that’s easier said than done, right? How do you keep up to date with the latest cybersecurity developments?
Follow The News
When it comes to cyber security, ignorance is not bliss – it’s a recipe for disaster. It’s imperative that you identify and follow a news feed that you can trust. By doing so, you can keep on top of any fresh threats that have emerged, learn lessons from other cyber attacks and pick up the latest tips and advice from influencers and experts in this field.
News from this sector really shouldn’t be seen as the preserve of IT specialists – the scale and nature of the threat suggest that this should be of interest to everyone. There’s a burgeoning band of podcasts available on the subject for people who prefer to digest content in this way too.
Bring Up The ‘Security Question’
If you think that installing an anti-virus program is enough, then you’re mistaken. Don’t just presume that you’re safe because you have this because this is merely the first line of defense to root out attacks. By adopting a safety first mindset you can ensure that the way you handle your data is less risky.
Whether it’s securing your Wi-Fi network at home, managing and updating your passwords on a regular basis or the way you collect, collate and analyze data throughthe point of sale software at work, continually ask yourself ‘is this safe?’ Just as ignorance isn’t bliss, complacency could prove your undoing. Place ‘security’ high on the list of credentials to consider when buying new software or hardware, don’t just go for the cheapest option.
Training
Even the experts are constantly having to refresh their understanding of the threat posed by cyber attacks. It pays to search out training opportunities, especially if you’re a business. You are, after all, only as safe as the people operating your software and systems and you don’t want to put the security of your business in the hands of someone who is unsure about what they are doing. Individuals and businesses alike can find free learning materials on Cybrary to help plug any knowledge gaps they have.
It’s Good To Talk
Cyber attacks are incredibly common – but people don’t often enough talk about their experiences. Perhaps you’re afraid or embarrassed to have been caught out? There’s no need to be. In fact, talking with friends and colleagues could really help you to stay safe. Pass on tips about new apps, good software, neat tips and tricks and any new cyber attack tactics you have come across and you can help to do your own bit to combat the criminals.
By keeping up to speed with security news, refreshing your training, sharing tips and tricks and adopting a safety first attitude you’ll give yourself the best possible chance of staying on top of cyber security developments and, best of all, safe.
What Is Network Security?
What Is Network Security? - CyberSecOp
Network security is an organization’s strategy and provisions for ensuring the security of its assets and all network traffic. Network security is manifested in an implementation of security hardware and software. For the purposes of this discussion, the following approach is adopted in an effort to view network security in its entirety.
What Is Network Security?
Policy
The IT Security Policy is the principle document for network security. Its goal is to outline rules for ensuring the security of organizational assets. Employees today often utilize several tools and applications to conduct business productively. Policy-driven from the organization’s culture supports these routines and focuses on safely enabling these tools for employees. Enforcement and auditing procedures for any regulatory compliance to which an organization is subject must be mapped out in the policies, and controls as well.
Types of network security
Access control
Not every user should have access to your network. To keep out potential attackers, you need to recognize each user and each device. Then you can enforce your security policies. You can block noncompliant endpoint devices or give them only limited access. This process is network access control (NAC).
Antivirus and antimalware software
"Malware," short for "malicious software," includes viruses, worms, Trojans, ransomware, and spyware. Sometimes malware will infect a network but lie dormant for days or even weeks. The best antimalware programs not only scan for malware upon entry, but also continuously track files afterward to find anomalies, remove malware, and fix damage.
Application security
Any software you use to run your business needs to be protected, whether your IT staff builds it or whether you buy it. Unfortunately, any application may contain holes, or vulnerabilities, that attackers can use to infiltrate your network. Application security encompasses the hardware, software, and processes you use to close those holes.
Behavioral analytics
To detect abnormal network behavior, you must know what normal behavior looks like. Behavioral analytics tools automatically discern activities that deviate from the norm. Your security team can then better identify indicators of compromise that pose a potential problem and quickly remediate threats.
Data loss prevention
Organizations must make sure that their staff does not send sensitive information outside the network. Data loss prevention, or DLP, technologies can stop people from uploading, forwarding, or even printing critical information in an unsafe manner.
Email security
Email gateways are the number one threat vector for a security breach. Attackers use personal information and social engineering tactics to build sophisticated phishing campaigns to deceive recipients and send them to sites serving up malware. An email security application blocks incoming attacks and controls outbound messages to prevent the loss of sensitive data.
Firewalls
Firewalls put up a barrier between your trusted internal network and untrusted outside networks, such as the Internet. They use a set of defined rules to allow or block traffic. A firewall can be hardware, software, or both. Cisco offers unified threat management(UTM) devices and threat-focused next-generation firewalls.
Intrusion prevention systems
An intrusion prevention system (IPS) scans network traffic to actively block attacks. Next-Generation IPS (NGIPS) appliances do this by correlating huge amounts of global threat intelligence to not only block malicious activity but also track the progression of suspect files and malware across the network to prevent the spread of outbreaks and reinfection.
Mobile device security
Cybercriminals are increasingly targeting mobile devices and apps. Within the next 3 years, 90 percent of IT organizations may support corporate applications on personal mobile devices. Of course, you need to control which devices can access your network. You will also need to configure their connections to keep network traffic private.
Network Segmentation
Software-defined segmentation puts network traffic into different classifications and makes enforcing security policies easier. Ideally, the classifications are based on endpoint identity, not mere IP addresses. You can assign access rights based on role, location, and more so that the right level of access is given to the right people and suspicious devices are contained and remediated.
Security information and event management
SIEM products pull together the information that your security staff needs to identify and respond to threats. These products come in various forms, including physical and virtual appliances and server software.
VPN
A virtual private network encrypts the connection from an endpoint to a network, often over the Internet. Typically, a remote-access VPN uses IPsec or Secure Sockets Layer to authenticate the communication between device and network.
Web security
A web security solution will control your staff’s web use, block web-based threats, and deny access to malicious websites. It will protect your web gateway on site or in the cloud. "Web security" also refers to the steps you take to protect your own website.
Wireless security
Wireless networks are not as secure as wired ones. Without stringent security measures, installing a wireless LAN can be like putting Ethernet ports everywhere, including the parking lot. To prevent an exploit from taking hold, you need products specifically designed to protect a wireless network.
Cyber Security, New York Fights Back to Prevent Financial System Take Down
New York is quietly working to prevent a major cyber attack that could bring down the financial system.
As hackers become more sophisticated and cyber attacks more routine, New York is on notice.
With a lack of leadership from the federal government, New York is one of the first states to implement new cyber regulations.
The state is quietly working to prevent a major cyber attack that could bring down Wall Street's financial system.
But even with the strictest cybersecurity regulations in the country, experts warn New York's efforts may still not be enough.
NEW YORK — Five months before the 9/11 attacks, US Secretary of Defense Donald Rumsfeld sent a memo to one of his advisers with an ominous message.
"Cyberwar," read the subject line.
"Please take a look at this article," Rumsfeld wrote, "and tell me what you think I ought to do about it. Thanks."
Attached was a 38-page paper, published seven months prior, analyzing the consequences of society's increasing dependence on the internet.
It was April 30, 2001. Optimistic investors and frenzied tech entrepreneurs were still on a high from the dot-com boom. The World Wide Web was spreading fast.
Once America's enemies got around to fully embracing the internet, the report predicted, it would be weaponized and turned against the homeland.
The internet would be to modern warfare what the airplane was to strategic bombers during World War I.
The paper's three authors — two PhD graduates and the founder of a cyber defense research center — imagined the damage a hostile foreign power could inflict on the US. They warned of enemies infecting computers with malicious code, and launching mass denial of service attacks that could bring down networks critical to the functioning of the American economy.
"[We] are concerned that US leadership, and other decision makers about Internet use, do not fully appreciate the potential consequences of the current situation," the report said. "We have built a network which has no concept whatsoever of national boundaries; in a war, every Internet site is directly on the front line. If we do not change course soon, we will pay a very high price for our lack of foresight."
The US government had a problem on its hands and it seemed a long ways from figuring out how to handle it.
More than 17 years later, that problem seems to have only gotten worse.
Follow the money
Willie Sutton, the notorious Brooklynite who spent his life in and out of prison, once told a reporter he robbed banks because that's where the money is. Computer hackers aren't so different.
In 2016, hackers attacked companies in the financial services sector more than companies in any other industry, according to IBM. Over 200 million financial records were breached that year, a 937% increase from 2015. And that's not including the incidents that were never made public.
As hackers become more sophisticated and cyber attacks more routine, New York is on notice. Home to the most valuable stock exchange on Earth, New York City is the financial capital of the world. When the market moves here, it moves everywhere.
So it was no surprise when in September 2016, Gov. Andrew Cuomo announced that the New York State Department of Financial Services (NYDFS) was gearing up to implement sweeping, first-of-their-kind cybersecurity regulations to protect the state's financial services industry — an unprecedented move no other state or federal agency had taken anywhere in the US.
Cybersecurity in New York's financial industry was previously governed by voluntary frameworks and suggested best practices. But the NYDFS introduced, for the first time, regulations that would be mandatory, including charging firms fines if they didn't comply.
Maria Vullo, the state's top financial regulator, told Business Insider that her No. 1 job is to protect New Yorkers.
"They're buying insurance. They're banking. They're engaging in financial transactions. And in each of those activities, they're providing their social security information, banking information, etc.," she said. "The companies that are obtaining that personal information from New Yorkers must protect it as much as possible because a breach of that information is of great consequence to the average New Yorker."
On March 1, the regulations turn a year old, although some of the rules are not yet in effect and will phase in overtime.
The NYDFS oversees close to 10,000 state-chartered banks, credit unions, insurance companies, mortgage loan servicers, and other financial institutions, in addition to 300,000 insurance licensees.
The combined assets of those organizations exceed $6 trillion, according to the NYDFS — and they're all in constant danger of being hacked.
Banks are vulnerable
In the summer of 2014, an American, two Israelis, and two co-conspirators breached a network server of JPMorgan Chase, the largest US bank.
They got hold of roughly 83 million customers' personal information, including names, addresses, phone numbers, and email addresses.
The hackers didn't steal any money from personal bank accounts, but that wasn't the point.
They wanted access to a massive trove of emails that they could use for a larger, separate money scam. In just three years, that operation netted the hackers more than $100 million.
The JPMorgan hack wasn't the end game. It was a piece of the puzzle.
The attack began with the simple theft of a JPMorgan employee's login credentials, which were located on a server that required just one password.
Most servers with sensitive information like a person's banking data require what's called multi-factor, or two-factor authentication.
But JPMorgan's security team had lapsed and failed to upgrade the server to include the dual password scheme, The New York Times reported at the time.
The attack, the breach, and the reputational damage that followed could have been avoided with tighter security. Instead, the hack went down as one of the largest thefts of customer data in US history.
"Banks are especially vulnerable," Matthew Waxman, a professor at Columbia Law School and co-chair of the Cybersecurity Center at the Columbia Data Science Institute, told Business Insider. "Disruption to the information systems on which banks rely could have shockwaves throughout the financial system, undermining public confidence in banking or knocking off line the ability to engage in commercial transactions."
That's the kind of catastrophic damage that worried the authors cited in Defense Secretary Rumsfeld's 2001 memo.
They weren't only concerned about stolen email addresses and social security numbers. They were worried about the fallout from such activity.
Banking works because consumers trust the system. But what if people lose trust?
Waiting until a catastrophe
News of impending cybersecurity regulations in New York in the fall of 2016 was both welcomed and shunned.
Some companies saw it as a chance to improve their own security standards while others complained of government overreach. Some were relieved to find they wouldn't have to make any adjustments to the way they operated. Others were overwhelmed by the heavy lifting they would have to do to comply.
How a company views the regulations depends in large part on its size. Bigger institutions with more cybersecurity professionals and more resources at their disposal tend to already have in place much of what the regulations require. Many smaller companies, which tend to be under-staffed and under-resourced, have a lot more work to do to catch up.
Jenny Cheng/Business Insider
The only additional thing Berkshire Bank has to do is sign off on its annual compliance form, which it sends to NYDFS to prove that it's doing everything it's supposed to be doing.
"We actually have to do nothing [new] from a compliance standpoint," the company's chief risk officer Gregory Lindenmuth told Business Insider.
While several cybersecurity consultants told Business Insider they acknowledge the NYDFS rules as a positive step in the right direction, they also point to a new law in Europe as a leading example of the role government has to play in protecting individuals' privacy rights and ensuring that companies secure consumers' personal information.
In 2016, the European parliament passed a law called the General Data Protection Regulation (GDPR) — landmark legislation that imposes millions of euros in fines on companies that do not adequately protect their customers' data.
Whereas the NYDFS regulations cover just one industry in one US state, the GDPR affects companies in all industries across all 28 member states of the European Union. Companies that do not report a data breach or fail to comply with the law more generally could be fined up to €20 million or 4% of its global revenue.
Matthew Waxman, the Columbia professor, says it's not surprising that the implementation of such a law remains far-fetched in the US.
"It's sometimes very difficult to get the government to take action against certain threats until a catastrophe takes place," Waxman said. "But that could change very suddenly if the banking system were knocked offline or another very major disruption to everyday life affected the lives and security of citizens on a massive scale."
But are the deterrents strong enough?
Data protection advocates calling for stricter cybersecurity regulations in the US are generally happy about the NYDFS rules.
For the first time, a state government is taking seriously the protection of consumer data, they say. It's giving companies in the financial sector an ultimatum: protect New Yorkers or face punishment.
"My big criticism of the regulations is there's no clear consequence for non-compliance," Thomas Boyden, the president of GRA Quantum and a cybersecurity expert who helps companies defend against cyber attacks, told Business Insider. "If companies don't feel like there's going to be any consequence for any action on their part, companies aren't going to take [the regulations] seriously."
In fact, for many companies, Boyden thinks "that's the default position."
Vullo, the head of the NYDFS, said she has the ability to fine companies that are not complying and is willing to exercise that authority, although how much that cost may be would depend case-by-case.
"I don't want this to be a punitive atmosphere, but obviously if institutions are not taking this seriously, then there will be consequences," she said. "But it's not the objective."
If anything, the objective is to make it clear that cyber threats are real and that New Yorkers and the companies that maintain their personal information are facing higher risks of attack.
Cybersecurity affects everyone, and Vullo said she hopes the regulations will help companies prioritize it.
"Everyone is part of our cybersecurity team," Theresa Pratt, the chief information security officer at Market Street Trust, a private trust company in New York, told Business Insider. "It doesn't matter what myself or my colleagues do from a technical perspective. If I have one user who clicks a bad link or answers a phisher's question over the phone, it's all for naught."
New York leading the way
The new rules have far-reaching implications beyond New York. A business in the state that has a parent company based in Germany, for example, still has to comply with the regulations.
This leaves some organizations in the precarious position of having to either restructure company-wide cybersecurity practices or build an entirely new and unique security apparatus that is specific to its New York offices.
"I do think that because of the scope of some of these regulations, they're kind of blurring the lines between countries and continents. I think we're going to see more and more of this," GreyCastle Security CEO Reg Harnish told Business Insider. The New York-based consulting firm is helping companies comply with the new regulations.
In the absence of leadership from the federal government on certain issues related to cybersecurity and data protection, states like New York are beginning to fill the void. Several cybersecurity experts told Business Insider that the NYDFS regulations could become a model for other industries or even policies at the national level.
Last year, at least 42 states introduced more than 240 bills or resolutions related to various cybersecurity issues, according to the National Conference of State Legislatures. And since the NYDFS rules took effect, financial regulators in Colorado and Vermont have followed New York's lead with cybersecurity regulations of their own.
Indeed, cyber experts have come a long way in better understanding the threats we face since Rumsfeld's dire cyberwar memo in 2001. But 17 years on, the former secretary of defense's concerns still seem as relevant as ever.
Perhaps the memo was a prescient warning — a warning that fell on deaf ears, but is not too late to address.
Secure Your Website, from Cyber Attacks
The average website was attacked 44 times a day during the last quarter of 2017, according to new research from security specialist SiteLock.
The company analyzed six million sites to identify trends in the behavior and tactics of attackers. Though the number of attacks represents a 25 percent decrease over the previous quarter, it still means a site could be attacked 16,000 times a year.
"A decrease in attacks does not mean that websites are safer. In fact, it may even be the opposite," says Neill Feather, president of SiteLock on the company's blog. "Hackers are constantly trying new avenues and even leveraging older tactics that continue to be successful. As our research shows, cybercriminals are now able to successfully breach a site with fewer, more targeted attacks. Now more than ever, businesses need to evaluate their current security posture and ensure they have both the right technology and a response plan in place should a hack occur."
Among other findings are that around one percent of sites sampled are infected with malware each week. Yet only 19 percent of infected sites are blacklisted by search engines. WordPress sites using plugins are twice as likely to be infected as sites that don’t employ a content management system. In addition, 46 percent of infected WordPress sites have the latest core updates. The average number of infected files per site increased by 0.8 percent to 309.
The malware being used is increasingly complex too. 51 of the malware found was categorized as Encoded Malware, meaning it was randomly generated or difficult to decode. These are often parts of groups of files called 'attack kits'. Backdoors made up 12 percent of files, resulting in more files being uploaded to infected sites.